체크포인트
Configure the Firewall
/ 30
Launch client VMs
/ 30
Launch Server VMs
/ 20
Create the Private Zone
/ 20
Cloud DNS: Traffic Steering using Geolocation Policy
- GSP1008
- Overview
- Setup and requirements
- Task 1. Enable APIs
- Task 2. Configure the firewall
- Task 3. Launch client VMs
- Task 4. Launch Server VMs
- Task 5. Setting up environment variables
- Task 6. Create the private zone
- Task 7. Create Cloud DNS Routing Policy
- Task 8. Testing
- Task 9. Delete lab resources
- Congratulations
- End your lab
GSP1008
Overview
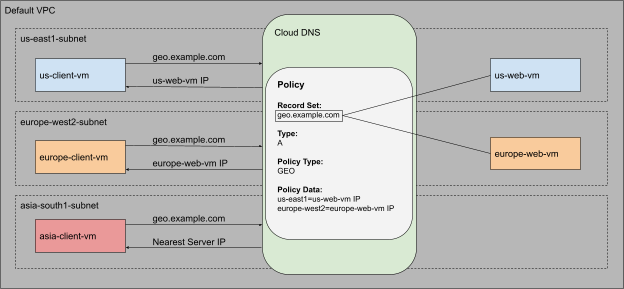
Cloud DNS routing policies enable users to configure DNS based traffic steering. A user can either create a Weighted Round Robin (WRR) routing policy or a Geolocation (GEO) routing policy. You can configure routing policies by creating special ResourceRecordSets with special routing policy values.
Use WRR to specify different weights per ResourceRecordSet for the resolution of domain names. Cloud DNS routing policies help ensure that traffic is distributed across multiple IP addresses by resolving DNS requests according to the configured weights.
In this lab you will configure and test the Geolocation routing policy. Use GEO to specify source geolocations and to provide DNS answers corresponding to those geographies. The geolocation routing policy applies the nearest match for the source location when the traffic source location doesn't match any policy items exactly.
What you learn
You will learn how to:
- Launch client VMs, one in each region
- Launch server VMs, one in each region except
- Create a private zone, for
example.com - Create a Geolocation routing policy using gcloud commands
- Test the configuration
Architecture
Use the default VPC network to create all the virtual machines (VM) and launch client VMs in 3 Google Cloud locations:
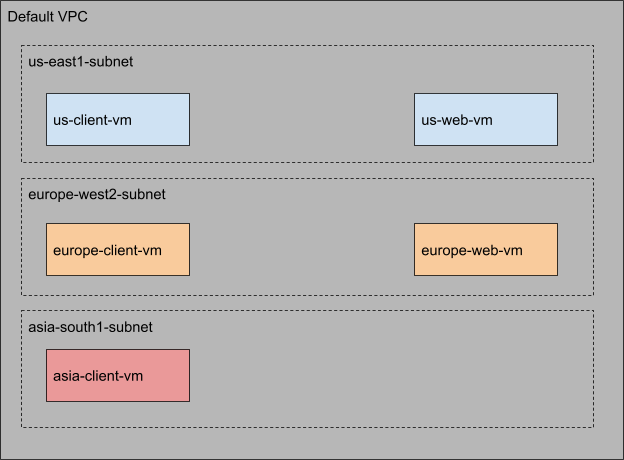
You will use Cloud DNS routing policies and create ResourceRecordSets for geo.example.com and configure the Geolocation policy to help ensure that a client request is routed to a server in the client's closest region.
Setup and requirements
Before you click the Start Lab button
Read these instructions. Labs are timed and you cannot pause them. The timer, which starts when you click Start Lab, shows how long Google Cloud resources will be made available to you.
This hands-on lab lets you do the lab activities yourself in a real cloud environment, not in a simulation or demo environment. It does so by giving you new, temporary credentials that you use to sign in and access Google Cloud for the duration of the lab.
To complete this lab, you need:
- Access to a standard internet browser (Chrome browser recommended).
- Time to complete the lab---remember, once you start, you cannot pause a lab.
How to start your lab and sign in to the Google Cloud console
-
Click the Start Lab button. If you need to pay for the lab, a pop-up opens for you to select your payment method. On the left is the Lab Details panel with the following:
- The Open Google Cloud console button
- Time remaining
- The temporary credentials that you must use for this lab
- Other information, if needed, to step through this lab
-
Click Open Google Cloud console (or right-click and select Open Link in Incognito Window if you are running the Chrome browser).
The lab spins up resources, and then opens another tab that shows the Sign in page.
Tip: Arrange the tabs in separate windows, side-by-side.
Note: If you see the Choose an account dialog, click Use Another Account. -
If necessary, copy the Username below and paste it into the Sign in dialog.
{{{user_0.username | "Username"}}} You can also find the Username in the Lab Details panel.
-
Click Next.
-
Copy the Password below and paste it into the Welcome dialog.
{{{user_0.password | "Password"}}} You can also find the Password in the Lab Details panel.
-
Click Next.
Important: You must use the credentials the lab provides you. Do not use your Google Cloud account credentials. Note: Using your own Google Cloud account for this lab may incur extra charges. -
Click through the subsequent pages:
- Accept the terms and conditions.
- Do not add recovery options or two-factor authentication (because this is a temporary account).
- Do not sign up for free trials.
After a few moments, the Google Cloud console opens in this tab.

Activate Cloud Shell
Cloud Shell is a virtual machine that is loaded with development tools. It offers a persistent 5GB home directory and runs on the Google Cloud. Cloud Shell provides command-line access to your Google Cloud resources.
- Click Activate Cloud Shell
at the top of the Google Cloud console.
When you are connected, you are already authenticated, and the project is set to your Project_ID,
gcloud is the command-line tool for Google Cloud. It comes pre-installed on Cloud Shell and supports tab-completion.
- (Optional) You can list the active account name with this command:
- Click Authorize.
Output:
- (Optional) You can list the project ID with this command:
Output:
gcloud, in Google Cloud, refer to the gcloud CLI overview guide.
Task 1. Enable APIs
Ensure that the Compute and the Cloud DNS APIs are enabled. In this section, you will enable the APIs manually, using gcloud commands.
Enable Compute Engine API
- Run the
gcloud services enablecommand to enable the Compute Engine API:
This command can take a few minutes to complete.
Enable Cloud DNS API
- Run the
gcloud services enablecommand to enable the Cloud DNS API:
This command can take a few minutes to complete.
Verify that the APIs are enabled
- Run the
gcloud services listcommand to list all the enabled APIs. We should seecompute.googleapis.comanddns.googleapis.comin the listed output.
Output:
Task 2. Configure the firewall
Before you create the client VMs and the web servers, you need to create two firewall rules.
firewall-rules create command can take a few minutes to complete. Please wait for the "Creating firewall...done" message before proceeding to the next step.- To be able to SSH into the client VMs, run the following to create a firewall rule to allow SSH traffic from Identity Aware Proxies (IAP):
Output:
- To allow HTTP traffic on the web servers, each web server will have a "http-server" tag associated with it. You will use this tag to apply the firewall rule only to your web servers:
Output:
Click Check my progress to verify the objective.
Task 3. Launch client VMs
Now that the APIs are enabled, and the firewall rules are in place, the next step is to set up the environment. In this section, you will create 3 client VMs, one in each region.
Launch client in
- Run the
gcloud compute instances createcommand to create the client VMs:
This command can take a few minutes to complete. Please wait for a "Created" message before moving to the next step.
Output:
Launch client in
- Run the following to create the client VMs:
Output:
Launch client in
- Run the following to create the client VMs:
Output:
Click Check my progress to verify the objective.
Task 4. Launch Server VMs
Now that the client VM's are up and running, the next step is to create the server VMs. You will use a startup script to configure and set up the web servers. As mentioned earlier, you will create the server VMs only in 2 regions:
- Run the
gcloud compute instances createcommand to create the server VMs. The compute instance create command can take a few minutes to complete. Please wait for a "Created" message before moving to the next step.
Launch server in
- Run the following to command:
Output:
Launch server in
- Run the following to command:
Output:
Click Check my progress to verify the objective.
Task 5. Setting up environment variables
Before you configure Cloud DNS, note the Internal IP addresses of the web servers. You need these IPs to create the routing policy. In this section, you will use the gcloud compute instances describe command to save the internal IP addresses as environment variables.
- Command to save IP address for the vm in
:
- Command to save the IP address for vm in
:
Task 6. Create the private zone
Now that your client and server VMs are running, it's time to configure the DNS settings. Before creating the A records for the web servers, you need to create the Cloud DNS Private Zone.
For this lab, use the example.com domain name for the Cloud DNS zone.
- Use the
gcloud dns managed-zones createcommand to create the zone:
Output:
Task 7. Create Cloud DNS Routing Policy
In this section, configure the Cloud DNS Geolocation Routing Policy. You will create a record set in the example.com zone that you created in the previous section.
Create
- Use the
gcloud beta dns record-sets createcommand to create the geo.example.com recordset:
You are creating an A record with a Time to Live (TTL) of 5 seconds. The policy type is GEO, and the routing_policy_data field accepts a semicolon-delimited list of the format "$${region}:$${rrdata},${rrdata}".
Output:
Verify
- Use the
dns record-sets listcommand to verify that thegeo.example.comDNS record is configured as expected:
The output shows that an A record with a TTL of 5 is created for geo.example.com, and the data matches our server set up in each region.
Output:
Click Check my progress to verify the objective.
Task 8. Testing
It's time to test the configuration. In this section, you will SSH into all the client VMs. Since all of the web server VMs are behind the geo.example.com domain, you will use cURL command to access this endpoint.
Since you are using a Geolocation policy, the expected result is that:
- The client in the US should always get a response from the
region. - The client in Europe should always get a response from the
region.
Testing from the client VM in
- Use the
gcloud compute sshcommand to log into the client VM:
- Follow prompts to SSH into the machine. When asked to enter the passphrase, leave the field blank and press the Enter key twice.
Once complete, the command line should change to "user_name@europe-client-vm:~$"
Output:
Use curl to access the web server
- Now that you are in the client VM, use the
cURLcommand to access thegeo.example.comendpoint. The loop is configured to run the command ten times with a sleep timer of 6 seconds:
Since the TTL on the DNS record is set to 5 seconds, a sleep timer of 6 seconds has been added. The sleep timer will make sure that you get an uncached DNS response for each cURL request. This command will take approximately one minute to complete.
The expected output is "Page served from:
- Run this test multiple times and analyze the output to see which server is responding to the request. The client should always receive a response from a server in the client's region.
Getting back to Cloud Shell
- Once you have run the test multiple times, exit the client VM in Europe by typing "
exit" in the VM's command prompt. This will bring you back to the Cloud Shell console.
Testing from the client VM in
Now perform the same test from the client VM in the US.
- Use the
gcloudcommand below to SSH into the us-client-vm:
- Use the
curlcommand to accessgeo.example.com:
-
Now analyze the output to see which server is responding to the request. The client should always receive a response from a server in the client's region. The expected output is "Page served from:
". -
Once you have run the test multiple times, exit the client VM in the US by typing "
exit" in the VM's command prompt.
Testing from the client VM in
So far you have tested the setup from
The Geolocation policy will apply a "nearest" match for source location when the source of the traffic doesn't match any policy items exactly. This means that the client in the
In this section, you will resolve the geo.example.com domain from the client VM in Asia and will analyze the response.
- SSH into the us-client-vm:
- Then access geo.example.com:
-
Analyze the output to see which server is responding to the request. Since there is no policy item for
, Cloud DNS will direct the client to the nearest server. -
Once you have run the test multiple times, exit the client VM in Asia by typing "
exit" in the VM's command prompt.
Task 9. Delete lab resources
Although all resources you used in this lab will be deleted when you finish, it is good practice to remove resources you no longer need to avoid unnecessary charges.
- The following
gcloudcommands will delete all the resources that were created in the lab:
Congratulations
In this lab you configured and used Cloud DNS routing policies with Geolocation routing policy. You also verified the configuration and behavior of the Cloud DNS routing policy by observing the HTTP response when accessing the web servers.
Next steps / Learn more
You can read more about Cloud DNS routing policies.
Google Cloud training and certification
...helps you make the most of Google Cloud technologies. Our classes include technical skills and best practices to help you get up to speed quickly and continue your learning journey. We offer fundamental to advanced level training, with on-demand, live, and virtual options to suit your busy schedule. Certifications help you validate and prove your skill and expertise in Google Cloud technologies.
Manual Last Updated October 12, 2023
Lab Last Tested October 12, 2023
End your lab
When you have completed your lab, click End Lab. Your account and the resources you've used are removed from the lab platform.
You will be given an opportunity to rate the lab experience. Select the applicable number of stars, type a comment, and then click Submit.
The number of stars indicates the following:
- 1 star = Very dissatisfied
- 2 stars = Dissatisfied
- 3 stars = Neutral
- 4 stars = Satisfied
- 5 stars = Very satisfied
You can close the dialog box if you don't want to provide feedback.
For feedback, suggestions, or corrections, please use the Support tab.
Copyright 2024 Google LLC All rights reserved. Google and the Google logo are trademarks of Google LLC. All other company and product names may be trademarks of the respective companies with which they are associated.
